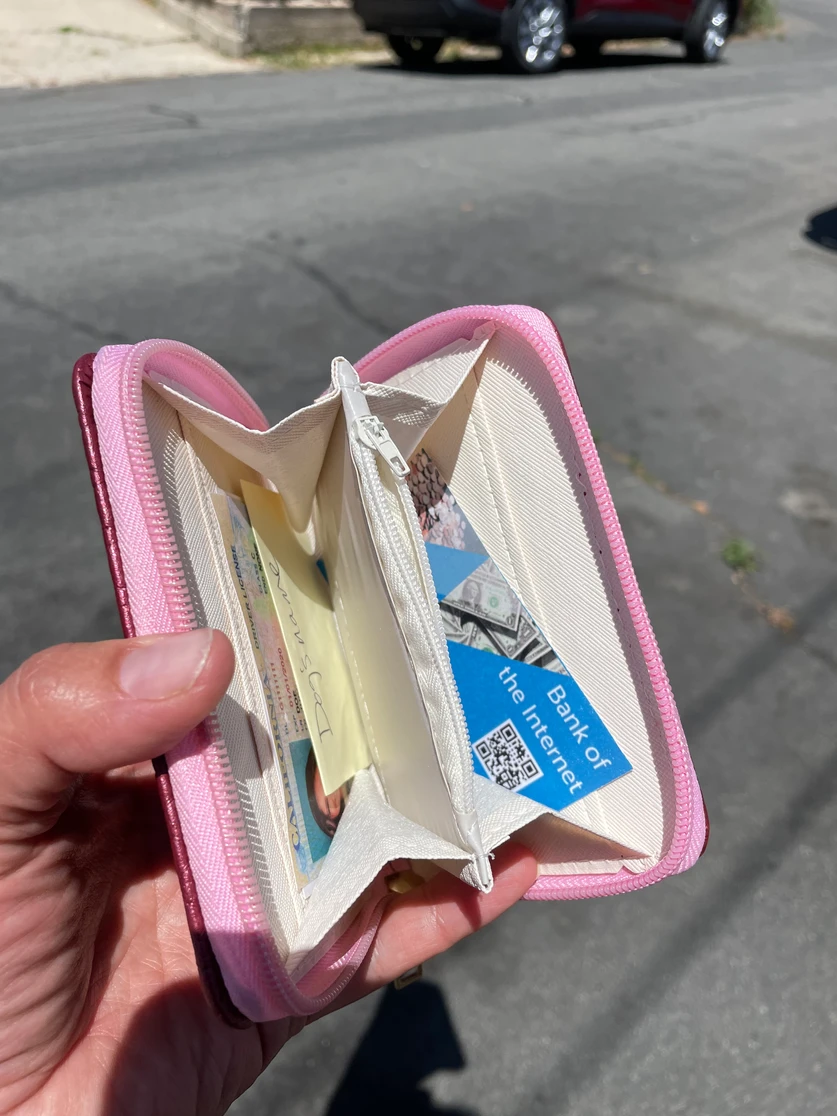
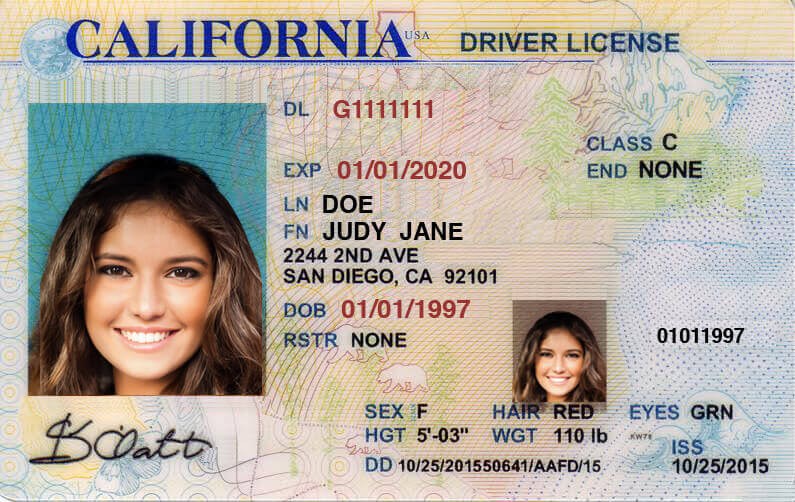
As your lovely mother walks out the door on this mother’s day, she backs out of the driveway to leave, only for you to find her wallet has fallen out of her purse and into the street. Grateful to be the one who has found it, you immediately imagine the worst case scenario, and decide to take a closer look to be sure she wouldn’t be able to be taken advantage of if someone else found it next time.
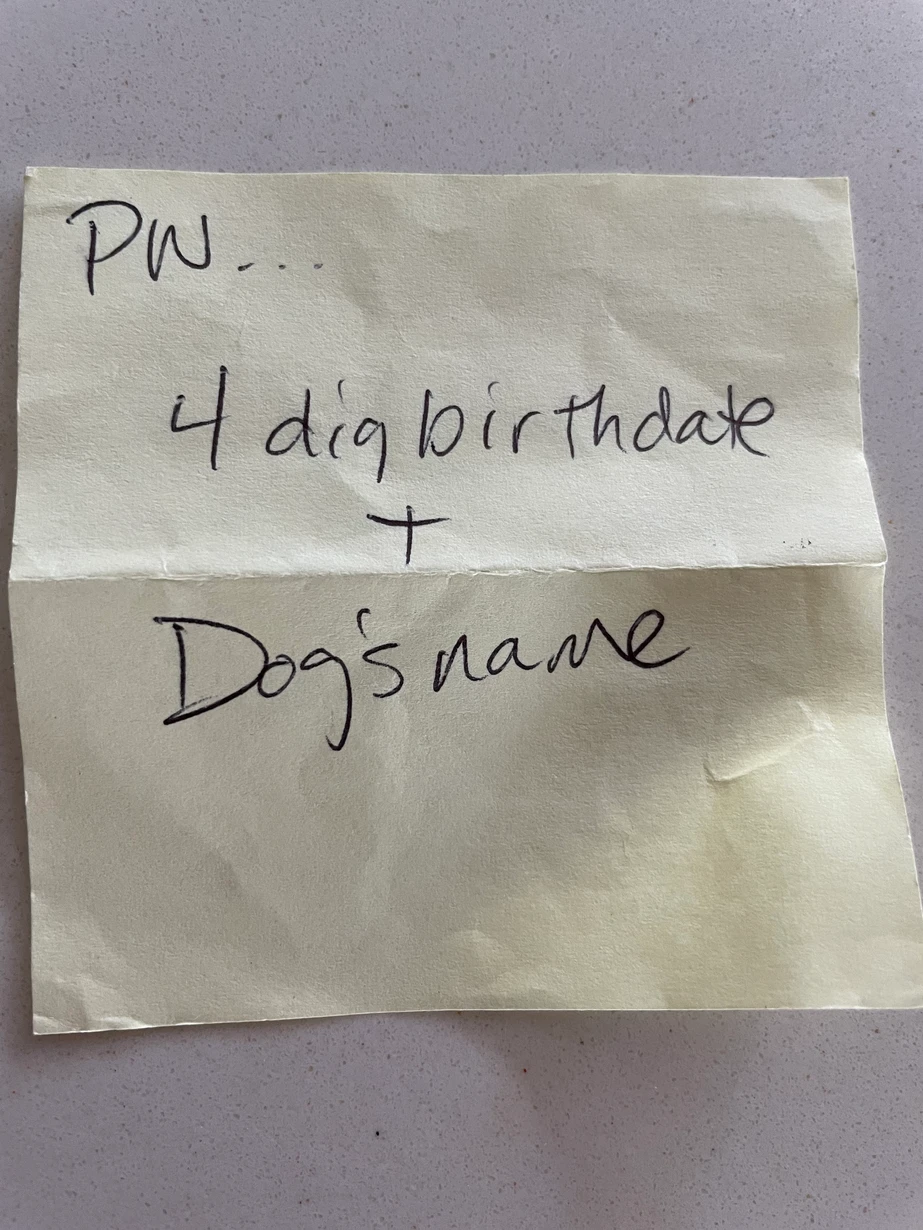
As you open the wallet you find the following contents, you are horrified to open the zipper pocket and see her password reminder post-it. Wondering what her level of vulnerability is, you are now drawn to see what a hacker may be able to accomplish if someone nefarious had found her wallet!
Use the items below found in the wallet and see what vulnerabilities you can find!
Did you make it to the congratulations page? If so we would love to hear from you. Share about your experience on social media by sharing a cyber tip you might give your mom to be sure she never gets hacked, and tag @packetman007 on Twitter, @austincyber on Facebook or Bill Alderson on LinkedIn.
Identity Security in the Age of Deepfakes
AI deepfakes and synthetic identity fraud have escalated identity theft well beyond stolen wallets. A lost driver's license once meant someone could impersonate you at a bank counter. Today, a single photograph combined with generative AI can produce video and voice deepfakes convincing enough to bypass biometric verification systems. Quantum computing threatens the cryptographic foundations of current identity verification, potentially rendering PKI-based digital IDs vulnerable before replacements are deployed.
The convergence of AI, cybersecurity, crypto, robotics, and quantum computing is redefining what identity means and how we protect it. Bill Alderson explores these converging threats on the Morpheus Cyber podcast.
1042