CISO: Day in the Life of CISO's Sameer Sait & Mustapha Kebbeh
In this session, two seasoned CISO's will talk about their experiences in leading and managing information security organizations. First they will discuss the day-to-day activities in the life of a CISO, followed by the more strategic and business-facing activities required to be successful in the role and finally delve into how external events impact both their strategic and tactical objectives.
Sameer Sait, Former CISO, Amazon/WFM
CISO Entrepreneur Investor Advisor
Sameer Sait is a seasoned information security leader with years of experience leading global, cross-functional teams. He recently exited the Information Security function for Amazon.com's largest subsidiary - Whole Foods Market. His global organization is responsible for IT governance/risk/compliance, security operations, threat intelligence, identity/access management, application and architecture security, eDiscovery & digital forensics. Prior to this, Sameer served as the VP, CISO at two Fortune 500 firms: Arrow Electronics and MassMutual.
Sameer is an advisor to a number of security startups and an active angel investor. His educational background includes a master’s degree from Carnegie-Mellon University and a bachelor’s degree from the University of Arizona.
Mustapha Kebbeh, CISO Brinks
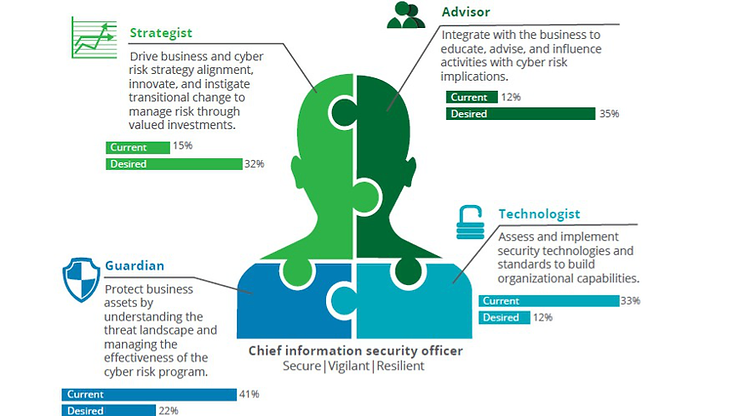
As Chief Information Security Officer for a global enterprise, I head vision and strategy for all IT cybersecurity, enterprise risk management, and IT enterprise architecture impacting 75,000 employees around the world. My goal is to protect information data and technologies from actual and potential threats, both internal and external to the organization.
This session was presented at a SecurityInstitute.com-sponsored cybersecurity conference.
Identity Under Siege: AI-Powered Credential Attacks
Identity and access management is the front line against a new class of AI-powered credential attacks. AI-generated phishing emails are now indistinguishable from legitimate communications. Deepfake voice and video can defeat multi-factor authentication that relies on human verification. Autonomous bots rotate through stolen credential databases at machine speed. IAM is no longer just an IT discipline — it is the security perimeter for the AI era. As quantum computing threatens the cryptographic foundations of current identity verification, the convergence Bill Alderson explores on the Morpheus Cyber podcast becomes essential reading for every GRC and IAM professional.
1033